Offering Network Installation For Your Present And Future Usage
Thinking about the complexity of networks plus the function networks play in one’s everyday activities, your ideal bet when organizing a home or business computer system configuration, is usually to employ a professional service for your system installation.
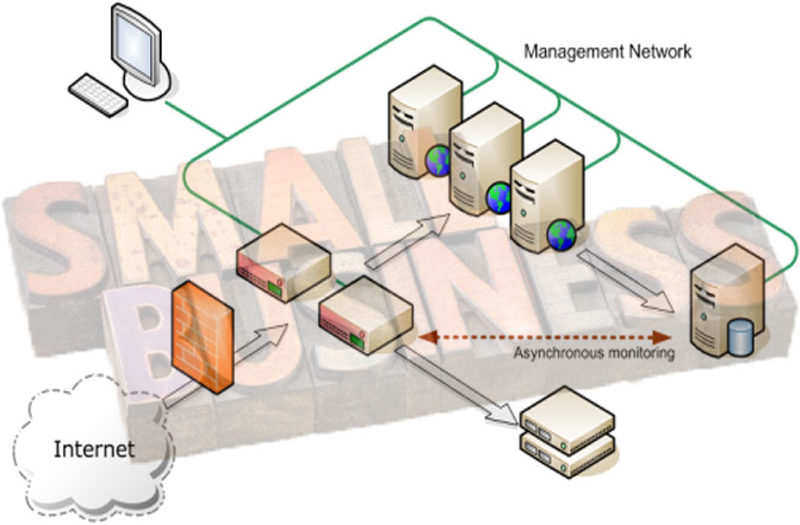
Before the actual installation, it’s essential to assess particular scenarios which will make sure that you
install a network that is adequate for nowadays but can simply accommodate your desires as your corporation grows. Mainly because creating a poor choice for the duration of this phase is detrimental to the achievement of your network installation, hiring an expert network installation service is also important.
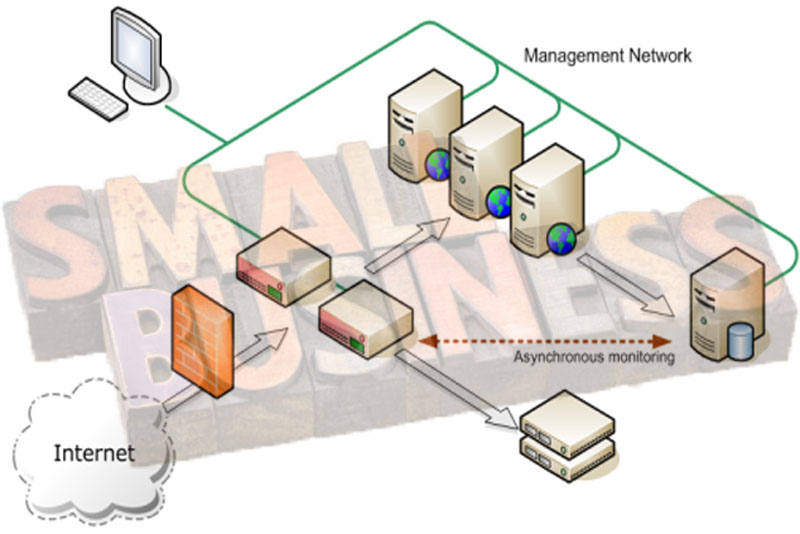
Usage
You can know who will use the network and what they will make use of the network for. This implies that for every location of the enterprise or every person in your home network, you may have to gather and document needs. Failing to obtain input from … Continue reading >>>