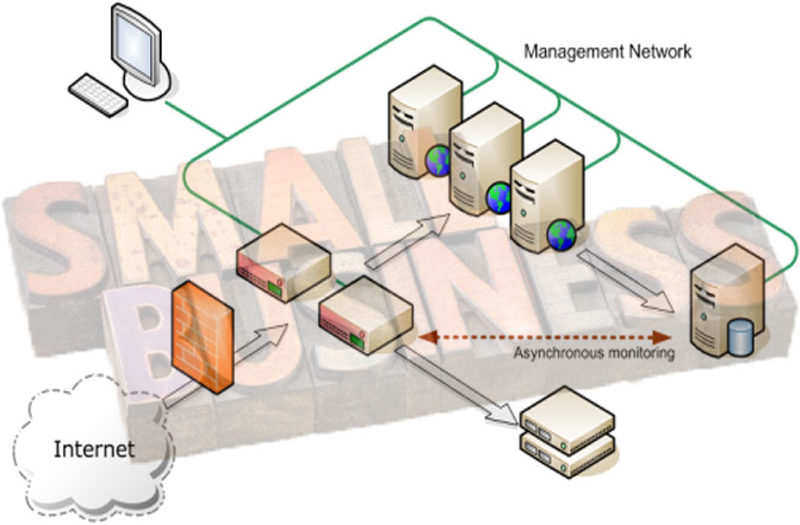
Basically designing small, medium, or enterprise class computer networks are principally similar. You need to design your private network infrastructure to provide the availability and reliability of network resources; network security system to protect your network resources against any types of threats, and secure global communication system. Small business computer network should include these three aspects: the private network; the end-point security system for internet threats protection; and a secure way in providing system communication with global internet.
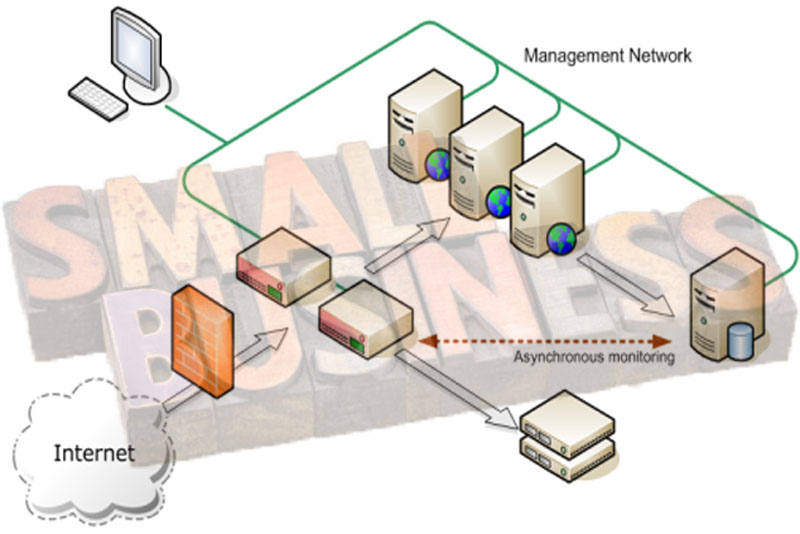
For example, in your business network you need to provide database application to support your finance management, and an email server to support your business communication, you allow authorized users to connect via internet from homes, or probably you need to link other branch offices via WAN cloud connection. Dig as much information as possible before designing your small business network. The following lists some areas you probably need to implement in your design.
Software Applications
You need to drill down the requirements each of the main element of your core business needs. For example, you need a database application to support your finance management. What application software to purchase, contact the vendor and ask them to provide a presentation about their product and see if their product can meet your finance need. How critical your application to support your business will be, if you don’t accept any downtime – you need to provide redundant servers and configure them as failover / failback system. You can dig more information to meet your business need regarding the finance management.
User Account Management
What about user account management? How do you manage the security of your network resources, who can access or deny certain resources and how they can access them? This will help you to design your logical infrastructure need, for example you need to implement Windows server with Active directory (AD) system which should be integrated with your DNS.
With AD infrastructure, you can create group policies that meet your security needs based on different level of user groups. If you implement a Windows server AD, you need to think about how to manage the patches. How all the computers update the Windows patches and other critical security update, will they download the patches direct from the internet or will you deploy a WSUS patches management system? With WSUS, you can manage all the computers within the network to download the Windows update from your WSUS server, not individually download direct from the internet. This will reduce the latency of your internet bandwidth.
Backup System
What about the backup system? How many data file servers are you going to deploy including the Email system? Will you install a tape drive backup system in each of the server or manage all the backup system centrally using Autoloader backup solution? When your business data grows, you need to implement such Autoloader backup system to centrally manage the backup of all the servers to reduce administration and cost overhead.
Network Security
What about endpoint security protection? When you provide the internet access for your users, how can you manage the security? We know that Internet is where all the bad and good things exist. Internet threats such as hackers and malware are evolved all the time to get smarter to detect and penetrate any vulnerabilities of your network system. How can you manage the internet threats, do you have security experts in taking care of your endpoint security system? Probably you need to implement UTM (unified Threat Management) appliance – an-all-in-one solution for your endpoint security system such as SonicWALL NSA 2400 network security appliance.
Email System
What about Email system? Will you manage your own Email system inside your private network? If so, you need to buy a domain name which represents your organization for example Your-Company. Com. You need to liaise with your ISP to host your domain record in their DNS server using one of your public IP address. You need to manage the firewall to allow the email traffic to flow in and out securely based on security policy of your organization.
Collecting data as much as possible regarding your small business computer network requirements is very essential before you can design the infrastructure to provide the availability and reliability of the network resources securely.