What Does A Computer Technician Do? (With Photographs)
 Student is accountable for performing extremely complicated computer system-associated technical perform working with specialized skills and information. Computer Technician is the only resource committed to supplying people interested in becoming a computer technician with unbiased data about distinctive degree and school solutions as effectively as profession, job and salary info. They may well pick to keep present by enrolling in professional instruction courses supplied by their employers or computer software and hardware vendors. 1 of the greatest techniques to get encounter beyond your classroom training is via an internship in the field. The above is by no suggests the only certification provided in personal computer technologies. An associate’s degree in a laptop-associated discipline might be all that is needed for other positions.
Student is accountable for performing extremely complicated computer system-associated technical perform working with specialized skills and information. Computer Technician is the only resource committed to supplying people interested in becoming a computer technician with unbiased data about distinctive degree and school solutions as effectively as profession, job and salary info. They may well pick to keep present by enrolling in professional instruction courses supplied by their employers or computer software and hardware vendors. 1 of the greatest techniques to get encounter beyond your classroom training is via an internship in the field. The above is by no suggests the only certification provided in personal computer technologies. An associate’s degree in a laptop-associated discipline might be all that is needed for other positions.
Because laptop technicians are so in demand, there are quite a few scholarships, grants, and other funds obtainable. Usually, the certification indicates that you have a specific level … Continue reading >>>

 If you are at house reading this then you are most likely connected to the Net. Combining the ideal of MPLS with the greatest of IP Safety enables us to develop high efficiency, safe and resilient wide area networks. No matter what your needs, Oxford Networks has the capacity to deal with your information demands, help you engineer for the future, and assistance you with a dedicated team of experts. 1 of the finest examples of a WAN is the Web: a WAN that grows larger day by day. In an outside setting you could have your Gateway unit mounted on the roof of a developing in the center of the region you want to cover.
If you are at house reading this then you are most likely connected to the Net. Combining the ideal of MPLS with the greatest of IP Safety enables us to develop high efficiency, safe and resilient wide area networks. No matter what your needs, Oxford Networks has the capacity to deal with your information demands, help you engineer for the future, and assistance you with a dedicated team of experts. 1 of the finest examples of a WAN is the Web: a WAN that grows larger day by day. In an outside setting you could have your Gateway unit mounted on the roof of a developing in the center of the region you want to cover.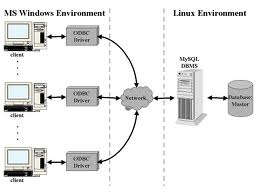 To answer all of this we very first have to figure out what the server is going to be utilized for. Appropriate backup procedures are critical for now, if you have room in your server and in your budget, you could want to slot in a second or even third hard drive. Some providers have really restrictive policies and prefer their customers not to do things like create servers others, like the outstanding , are thrilled to have adventurous customers.
To answer all of this we very first have to figure out what the server is going to be utilized for. Appropriate backup procedures are critical for now, if you have room in your server and in your budget, you could want to slot in a second or even third hard drive. Some providers have really restrictive policies and prefer their customers not to do things like create servers others, like the outstanding , are thrilled to have adventurous customers. Professionals at our National Testing and Investigation Center tested 164 models in computers to see which ones perform greatest. You will also possibly have to have to buy accessories such as a gaming keyboard , a gaming mouse and a joystick If you do video editing or graphic style, you’ll need a desktop with a potent CPU, lots of memory and a huge, quick challenging drive. Apple computers of course run the OS X operating method that is incredibly unique from Windows.
Professionals at our National Testing and Investigation Center tested 164 models in computers to see which ones perform greatest. You will also possibly have to have to buy accessories such as a gaming keyboard , a gaming mouse and a joystick If you do video editing or graphic style, you’ll need a desktop with a potent CPU, lots of memory and a huge, quick challenging drive. Apple computers of course run the OS X operating method that is incredibly unique from Windows.






